Prefatory Note — The Policy Context
The Prime Minister’s appeal for enabling Work from Home, hybrid working arrangements, online meetings and reduced travel wherever operationally feasible deserves a positive response from employers. WFH is not merely a welfare measure — it reduces urban congestion, carbon footprint, and commuting costs, and can demonstrably improve productivity when implemented thoughtfully.
Employers who embrace WFH should do so, however, through a written WFH policy that is legally reviewed and addresses the full spectrum of applicable Indian law — including Indian labour laws (Factories Act, Industrial Disputes Act, Shops and Establishments Acts as applicable to the state of operation), employment contracts, standing orders where applicable, POSH obligations (Prevention of Sexual Harassment at the Workplace Act, 2013), applicable social security obligations (EPF, ESI, gratuity), and the Digital Personal Data Protection Act, 2023.
The DPDP dimension of Work from Home, particularly in relation to what employee monitoring an employer may or may not lawfully conduct, forms the subject matter of this advisory. Although the DPDP framework is being implemented in phases and is expected to become fully effective from May 13, 2027, organisations should use the transition period to align their WFH monitoring practices with the principles of notice, purpose limitation, data minimisation, proportionality, security and employee privacy.
Setting the Legal Framework
In the DPDP context, the employer is the Data Fiduciary — the entity that determines the purpose and means of processing personal data (Section 2(i), DPDP Act). The employee is the Data Principal — the individual to whom the personal data relates (Section 2(j)). Every monitoring mechanism deployed in a WFH environment involves the collection and processing of the employee’s personal data, and in several cases, personal data of other household members who are entirely outside the employment relationship.
The key lawful basis available to employers under the DPDP Act for processing employee data without requiring consent is Section 7(i) — which permits processing for purposes of employment or those related to safeguarding the employer from loss or liability, such as prevention of corporate espionage, maintenance of confidentiality of trade secrets, intellectual property, classified information, or provision of any service or benefit sought by a Data Principal who is an employee.
This is a legitimate use — but it is not a blanket surveillance licence. It is bounded by two fundamental constraints that apply throughout the DPDP Act.
The first is data minimisation and necessity: under Section 6(1), processing must be limited to personal data that is necessary for the specified purpose. The same principle is expressed in the Second Schedule to the DPDP Rules, which requires processing to be limited to such personal data as is necessary for such uses or achieving such purposes.
The second is proportionality: the Puttaswamy judgment (Justice K.S. Puttaswamy (Retd.) vs Union of India, 2018, included in the project knowledge base) lays down the constitutional standard — a limitation of a fundamental right is permissible only if it is designated for a proper purpose, the measures are rationally connected to that purpose, the measures are necessary in that there are no alternative measures that may similarly achieve the same purpose with a lesser degree of limitation, and there is a proper balance between the importance of the purpose and the importance of the right being limited. This proportionality doctrine — not merely statutory compliance — governs what an employer may permissibly do in a WFH monitoring context.
Issue 1 — Screen Activity Monitoring and Recording
What is collected: Application usage, websites visited, documents accessed, communications composed, work patterns, keystroke sequences, and browsing behaviour.
DPDP Analysis:
Screen monitoring limited to work-device activity during designated working hours has a defensible basis under Section 7(i) for the purpose of preventing corporate data leakage, protecting trade secrets, and ensuring compliance with confidentiality obligations. However, the following distinctions are critical.
Monitoring which applications are open, whether corporate systems are being accessed, and whether DLP alerts are triggered — these are proportionate to the stated purpose. They constitute access logs and activity metadata, not a reproduction of content.
Full-day screen recording — capturing every pixel of everything displayed on an employee’s screen continuously — is disproportionate. It records personal communications, personal browser activity, medical or financial information briefly displayed, and the content of confidential client communications. The Puttaswamy proportionality test asks whether there is a less intrusive measure that achieves the same purpose. The answer here is yes — DLP alerts, access logs, and application monitoring achieve the security objective without wholesale content surveillance.
Keystroke logging is particularly invasive. It captures passwords, personal messages, draft communications subsequently deleted, and information entirely unrelated to work. No legitimate employment purpose requires the capture of every keystroke. It fails the proportionality test.
Notice obligation: Even where Section 7(i) applies and consent is not required, Section 5 of the DPDP Act requires the employer to give the employee a notice describing the personal data being collected and the purpose. A monitoring policy must be explicitly communicated in clear and plain language — not merely buried as a clause in an employment agreement signed on joining.
Assessment: Limited, purpose-specific screen activity monitoring is defensible. Full-day screen recording and keystroke logging are disproportionate and non-compliant.
Issue 2 — Webcam Open During Working Hours (Continuous Video Feed)
What is collected: Real-time visual data of the employee, their home environment, family members, and potentially other individuals who happen to be present.
DPDP Analysis:
A continuously open webcam during working hours collects several distinct categories of personal data simultaneously, each with a distinct legal problem.
The employee’s own image is personal data under Section 2(t). Continuous live video of a person in their home environment — revealing health indicators, emotional state, domestic circumstances, and living conditions — goes well beyond what is necessary to verify that work is being performed. Login activity, task completion, and access logs establish work activity without visual surveillance of the employee’s home.
Far more seriously, the webcam captures the personal data of household members — family, children, domestic workers — who are entirely outside the employment relationship and have given no consent whatsoever. They are Data Principals under the Act with full rights. The employer has no lawful basis — neither consent under Section 6 nor legitimate use under Section 7(i) — to collect their personal data. Section 7(i) is expressly limited to employment purposes; it does not extend to surveillance of third parties who happen to share the employee’s home.
The presence of children in the webcam feed creates an additional dimension. Section 9 of the DPDP Act requires verifiable parental consent before processing the personal data of a child under eighteen years of age. A household webcam that captures a child in the background is processing a child’s personal data without any consent mechanism at all.
Assessment: Continuous webcam monitoring during working hours is legally indefensible under the DPDP Act. It collects the personal data of third parties who have given no consent, captures children’s data in violation of Section 9, and fails the proportionality test even for the employee’s own data. This practice must be discontinued.
Issue 3 — Periodic Photographs Captured via Webcam
What is collected: Timestamped still facial images of the employee at regular automated intervals.
DPDP Analysis:
A facial photograph is unambiguously personal data. Periodic automated facial photographs, particularly when used for identity verification or attendance confirmation, constitute biometric data processing. The Puttaswamy judgment extensively addresses biometric data protection internationally, noting that facial scans require explicit consent and robust safeguards — principles consistent with the DPDP Act’s consent framework.
If the employer relies on Section 7(i), it must demonstrate that periodic facial photograph capture is necessary to prevent corporate espionage or safeguard trade secrets. This argument is very difficult to sustain. Login event logs, VPN connection records, and access logs establish that an authorised employee is operating the device — without requiring the capture and storage of biometric-level facial images at regular intervals.
If the employer instead relies on employee consent under Section 6, that consent must be free, specific, informed, unconditional, and unambiguous. The Puttaswamy judgment and DPDP consent jurisprudence recognise that consent given in an employment context — where an employee may fear job loss for withholding consent — is of questionable freedom. Consent embedded in a joining formality cannot satisfy the “free” requirement of Section 6(1).
The retention of these timestamped photographs over months or years represents a significant and growing database of biometric personal data, subject to Rule 8’s erasure obligations and Rule 6’s security requirements.
Assessment: The highest-risk element of WFH monitoring. Periodic facial photograph capture via webcam is biometric data processing that fails both the proportionality test under Section 7(i) and the free consent standard under Section 6(1). This practice carries acute DPDP compliance risk and must be discontinued.
Issue 4 — IP Address Capture and Tracking
What is collected: The employee’s home IP address, from which approximate residential location and internet service provider can be derived.
DPDP Analysis:
An IP address is personal data under Section 2(t). A home IP address additionally reveals information about the employee’s private residence. Two distinct use cases must be separated.
IP address for access authentication — verifying that a VPN or corporate system connection originates from an authorised device — has a clear and defensible basis under Section 7(i). This is consistent with the CERT-In Elemental Cyber Defense Controls (ACIM.1, ACIM.2), which require unique user IDs and role-based access controls. Using IP as an authentication signal in this context is proportionate.
Continuous tracking and storage of home IP addresses over time — correlating them to build location patterns, monitoring for address changes, or retaining them as a surveillance dataset — has no proportionate justification under the legitimate use basis. It constitutes location surveillance of an employee’s private residence, with no rational connection to the purpose of protecting trade secrets or corporate data.
Additionally, an employer who stores a database of all employees’ home IP addresses creates a significant breach risk. If that database is compromised, the residential network details of every WFH employee are exposed — creating a real-world security risk for the employees themselves that the employer, as Data Fiduciary, is responsible for preventing under Rule 6(1).
Assessment: IP capture for authentication is permissible. Continuous tracking, profiling, or retention of home IP addresses as a surveillance instrument is disproportionate and non-compliant.
Issue 5 — Aggregation and Profiling
What is collected: The combination of screen data + webcam feed + facial photographs + keystroke logs + IP address + application usage = a comprehensive behavioural profile of the employee in their home environment.
DPDP Analysis:
Each element of the monitoring regime creates a data exposure. But the aggregation of these elements into a combined profile is qualitatively more invasive than any single element. The Puttaswamy judgment specifically addresses informational privacy as a distinct constitutional right — the right to control what information about oneself is collected, aggregated, and used by others.
The aggregated profile reveals not just work activity but health patterns (movement in webcam), domestic relationships (household members visible), financial circumstances (home environment), and psychological state (work patterns and response times). None of this is necessary for employment management. It is behavioural surveillance that goes far beyond the employer’s legitimate interests under Section 7(i).
Assessment: Behavioural profiling through data aggregation in a WFH context has no valid lawful basis under the DPDP Act. It is disproportionate, exceeds any employment purpose, and constitutes a systematic interference with the employee’s informational privacy.
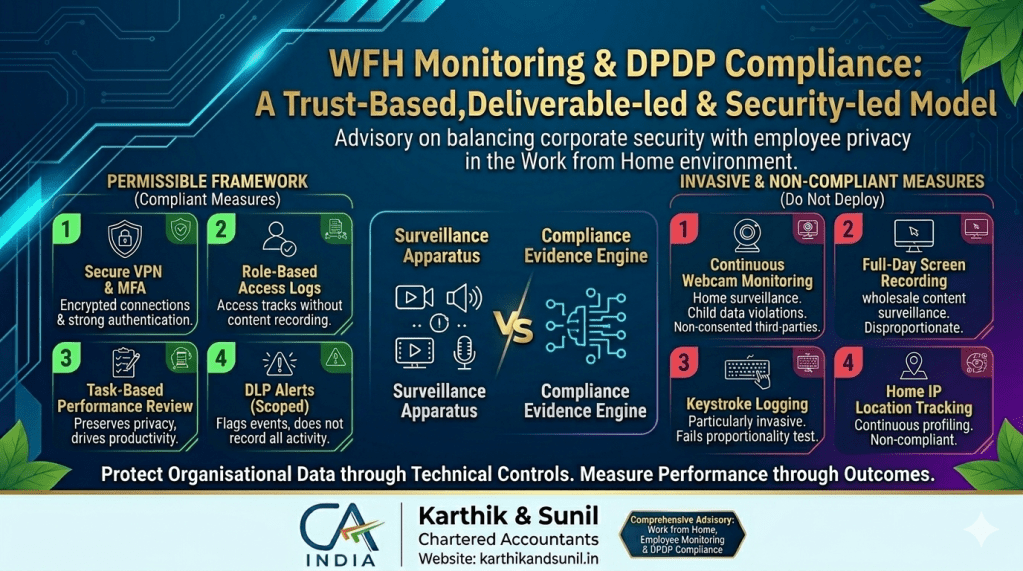
What the Employer Should Do — The Permissible Framework
Employers have a genuine and legitimate interest in protecting confidential information, trade secrets, intellectual property, customer data, and business systems. The DPDP Act fully recognises this under Section 7(i). The question is not whether to protect these interests but how — through measures that are proportionate, transparent, and respectful of the employee’s privacy in their home.
Recommended measures that are defensible under Section 7(i):
Secure VPN access — all WFH connections should be routed through a corporate VPN, ensuring encrypted transmission and access authentication without exposing the employee’s home network. MFA for all corporate systems, particularly those accessing customer data, financial records, or intellectual property. Role-based access control (RBAC) ensuring employees can access only the data their role requires. Access logs and audit trails showing which systems were accessed, when, and by whom — without recording the content of what was viewed. DLP (Data Leakage Prevention) alerts triggered when confidential data is transmitted outside authorised channels — flagging the event, not recording all activity. Device management policies governing corporate devices used for WFH, including remote wipe capability in the event of loss or separation. Task-based performance review and deliverable tracking — the most privacy-preserving and effective form of WFH productivity management, requiring no personal data beyond work outputs.
Measures that should not be deployed without strict necessity, proportionality, explicit notice, legal review, and a valid lawful basis:
Continuous webcam monitoring during working hours. Periodic automated facial photograph capture. Full-day screen recording. Keystroke logging. Home environment surveillance of any kind. Continuous home IP address tracking or location profiling. Behavioural profiling through data aggregation.
For any such measure that an employer nonetheless believes is strictly necessary for a specific, documented security purpose, the following conditions must all be met before deployment: a written documented justification of strict necessity, a proportionality assessment demonstrating no less intrusive alternative exists, a standalone clear and plain notice to employees specifying exactly what is collected, how it is stored, who can access it, for how long, and what rights the employee has, legal review of the lawful basis, defined retention and erasure schedules under Rule 8, and a grievance mechanism under Section 13 through which employees can raise objections.
The Preferred WFH Governance Model
The preferred model for WFH governance under DPDP is trust-based, deliverable-based, and security-led — not surveillance-led.
Trust-based: employees are presumed to be performing their duties unless there is a specific, documented reason to investigate otherwise. Surveillance is not a substitute for management.
Deliverable-based: performance is measured by outputs, outcomes, and quality of work — not by hours of screen visibility or number of keystrokes. This is both more legally defensible and more effective at driving actual productivity.
Security-led: the employer’s legitimate concerns about data security and IP protection are addressed through robust technical controls — VPN, MFA, RBAC, DLP, access logs — that protect the organisation’s assets without surveilling employees’ homes.
Summary Assessment Table
| WFH Practice | Lawful Basis Available | DPDP Status | Recommendation |
| Secure VPN access | Section 7(i) ✅ | Compliant | Implement as standard |
| MFA for all systems | Section 7(i) ✅ | Compliant | Implement as standard |
| Role-based access control | Section 7(i) ✅ | Compliant | Implement as standard |
| Access logs and audit trails | Section 7(i) ✅ | Compliant | Implement with retention schedule |
| DLP alerts (not full recording) | Section 7(i) ✅ | Compliant | Implement as standard |
| Task/deliverable-based review | No personal data | Preferred model | Implement as primary PM tool |
| Limited screen activity monitoring | Section 7(i) — conditional | Defensible if scoped | Limit to access metadata only |
| Full-day screen recording | No valid basis | Non-compliant | Do not deploy |
| Keystroke logging | No valid basis | Non-compliant | Do not deploy |
| Continuous webcam monitoring | No valid basis | Non-compliant | Do not deploy |
| Periodic webcam photographs | No valid basis | Non-compliant — biometric data | Do not deploy |
| Home IP continuous tracking | No valid basis | Non-compliant | Authentication use only |
| Behavioural profiling | No valid basis | Non-compliant | Do not deploy |
The Bottom Line
WFH is now policy-positive, PM-endorsed, and legally permissible. It is a legitimate, productivity-enhancing, environmentally responsible mode of working that Indian employers should embrace wherever operationally feasible.
The monitoring architecture that accompanies it, however, must be minimal, transparent, proportionate, labour-law compliant, and privacy-preserving.
An employer who enables WFH while deploying continuous webcam surveillance, periodic facial photographs, keystroke logging, and full-day screen recording has not implemented WFH — it has installed a surveillance apparatus inside the employee’s home. That is not what the PM’s appeal envisioned, it is not what good management requires, and it is not what Indian law — including the DPDP Act — permits.
The right model is this: protect the organisation’s data and systems through robust technical controls. Measure performance through outputs and outcomes. Trust the employee with the dignity of their private home environment. And build the WFH policy on a legal foundation that will withstand scrutiny — from the Data Protection Board, from employees who know their rights, and from a workforce that will perform best when it is trusted rather than surveilled.
Source note: All DPDP analysis is derived from the Digital Personal Data Protection Act, 2023 (Sections 2(i), 2(j), 2(t), 2(u), 5, 6, 7(i), 8, 9, 12, 13), the DPDP Rules, 2025 (Rules 6, 8, Second Schedule), the Justice K.S. Puttaswamy (Retd.) vs Union of India Supreme Court judgment (2018) on the right to privacy and proportionality doctrine, and the CERT-In Elemental Cyber Defense Controls for MSMEs (Version 1.0, dated 01.09.2025). References to labour law, POSH, EPF, ESI and Shops and Establishments requirements.
Disclaimer
This note is for general informational purposes only and should not be treated as legal opinion or professional advice. The applicability of Work from Home, employee monitoring, DPDP Act requirements, and labour law obligations may vary based on the facts, sector, state laws, employment terms, and internal policies.
Organisations should obtain a specific legal opinion from a qualified advocate / labour-law expert / data-protection professional before implementing or relying on any Work from Home or employee monitoring policy.
CA.Sunil E
Partner
